Resource Center
Learn More About Continuous DDoS Vulnerability Management
International Bank Chooses RADAR™ to Prevent Damaging DDoS Attacks

Financial Services Provider Slashes DDoS Risk from 50% to under 15%
Enhance Microsoft Azure DDoS Protection with MazeBolt RADAR
AI-Powered Cyber Threats and the Future of DDoS Defense
Robust DDoS Defense: A Guide for Network Professionals
What Most DDoS Protection Vendors Don’t Want You to Know
Cyber Awareness for Kids: Cyber Heroes and the DDoS Defense
A Comprehensive Guide to SEC Cyber Risk Management
Top 10 DDoS Attacks That Can Bring Down Your Business
The Essential Guide to Optimizing your DDoS Protection
7 Tips to Configuring Your Network and Preventing DDoS Attacks
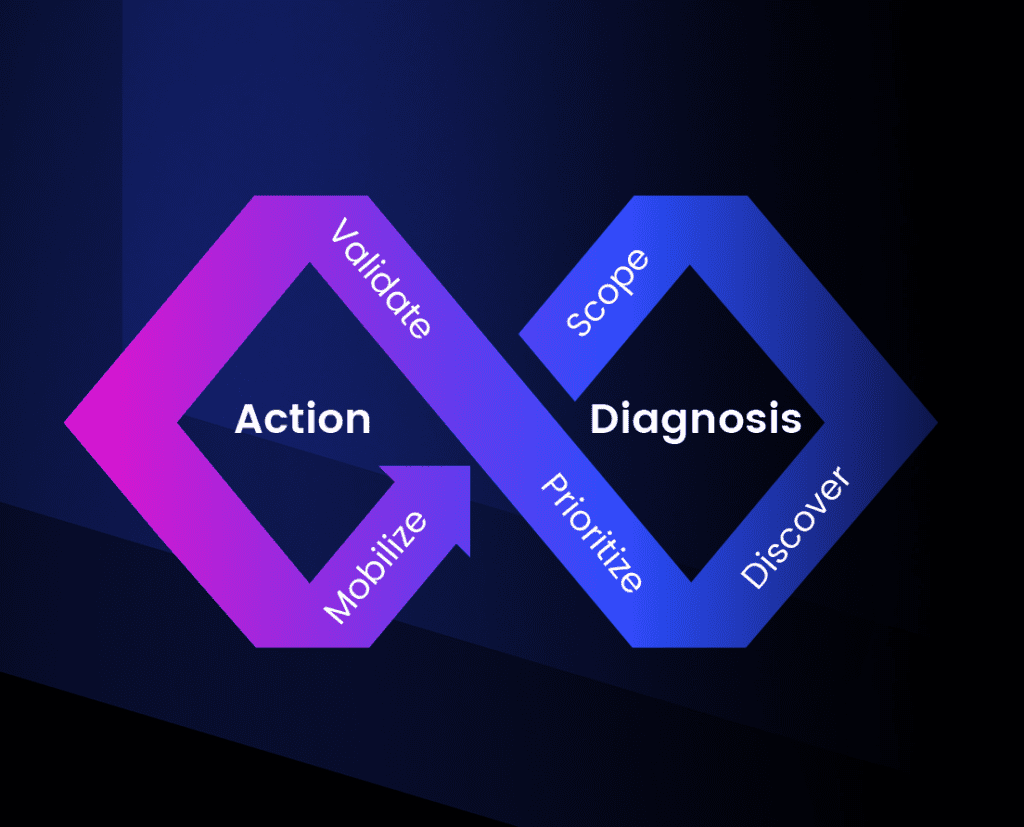
Infographic: Put Business Continuity First with CTEM

Infographic: Time is Running Out! DORA Enforcement Starts January 2025
Frost & Sullivan Report: Ongoing Vulnerability Testing for DDoS Protection

Ensuring Business Continuity in the Face of DDoS Threats

Webinar – How to Validate Akamai, Radware, Cloudflare DDoS Protections

Live Demo Webinar: Experience 24/7 DDoS Vulnerability Management in Action

RSAC2025 interview with Matthew Andriani, CEO and Founder at Mazebolt Technologies

Mazebolt x F5: Closing the Gaps in Cybersecurity Defense – RSAC 2025

Webinar: DDoS Crisis: The Hidden Downtime Threat & Why Protections Fail

Webinar: The Rising Threat of AI-Enhanced DDoS Attacks and How to Combat Them

Webinar Red Alert: Crippling DDoS Attacks Strike Europe
Which Threat Actors are Behind DDoS Attacks on Democratic Elections?
Introducing DDoS Vulnerability Management for Azure DDoS Protection with MazeBolt
The Problem of DDoS Attacks and the Vulnerabilities That Won’t Go Away
Non-Disruptive, Full-Coverage DDoS Testing with Zero Downtime
AI-Powered DDoS Vulnerability Detection and Mitigation

MazeBolt DTR | AI-based DDoS threat rating platform
Building Resilience in the DDoS War – Live Presentation