Blog
The IT Guide to DDoS: Layer 4 – Everything You Need to Know (Part 2)
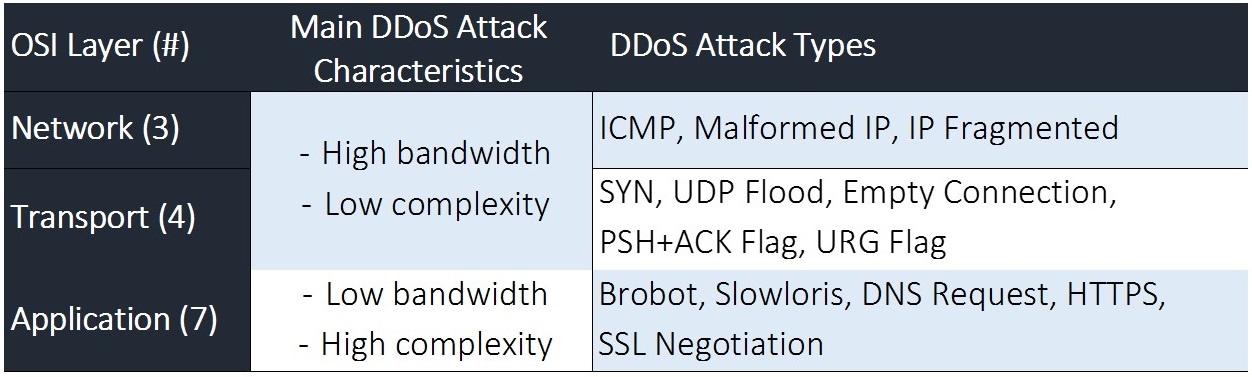
Learn how Layer 4 DDoS attacks target vulnerabilities in transport layer protocols like TCP and UDP to cause significant disruption without requiring vast amounts of traffic. Explore key attack types such as SYN floods, UDP floods, and ACK floods, and how to mitigate these threats.

Insights for Cybersecurity Awareness Month: 3 Tips on DDoS Resilience
The IT Guide to DDoS: Layer 3 – What You Need to Know (Part 1)

Doing Business in the EU? October 17 is the NIS2 Deadline

Frost & Sullivan Report: Continuous DDoS Vulnerability Testing is Key
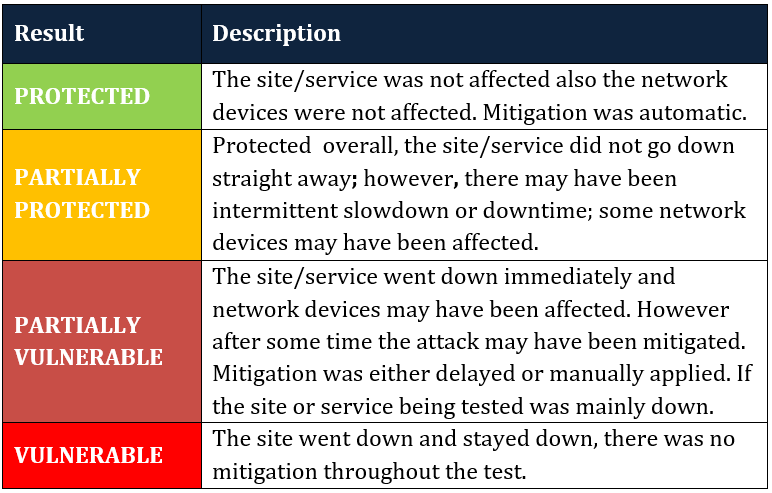
Put Your DDoS Protection to the Test

The Real Costs of DDoS Attacks Against the Enterprise

Yes, They ARE Out to Get You – And It’s Going to Cost You
Mind the Gap, the DDoS Mitigation Gap!
Your DDoS Attack May be Coming Soon – Three Types to Expect
The Attack Starts Now (This is Only a Drill)

Your DDoS Protection System Doesn’t Work. Here’s Why.