Blog
Advancing Enterprise DDoS Defense: MazeBolt RADAR’s 2024 Feature Review
2024 Year in Review: MazeBolt RADAR enhanced DDoS simulations, expanded attack coverage, improved performance, and added intuitive features for better security. Read more
Advancing Enterprise DDoS Defense: MazeBolt RADAR’s 2024 Feature Review
2024 Year in Review: MazeBolt RADAR enhanced DDoS simulations, expanded attack coverage, improved performance, and added intuitive features for better security.

5 DDoS Attacks That Your DDoS Mitigation May Not Prevent
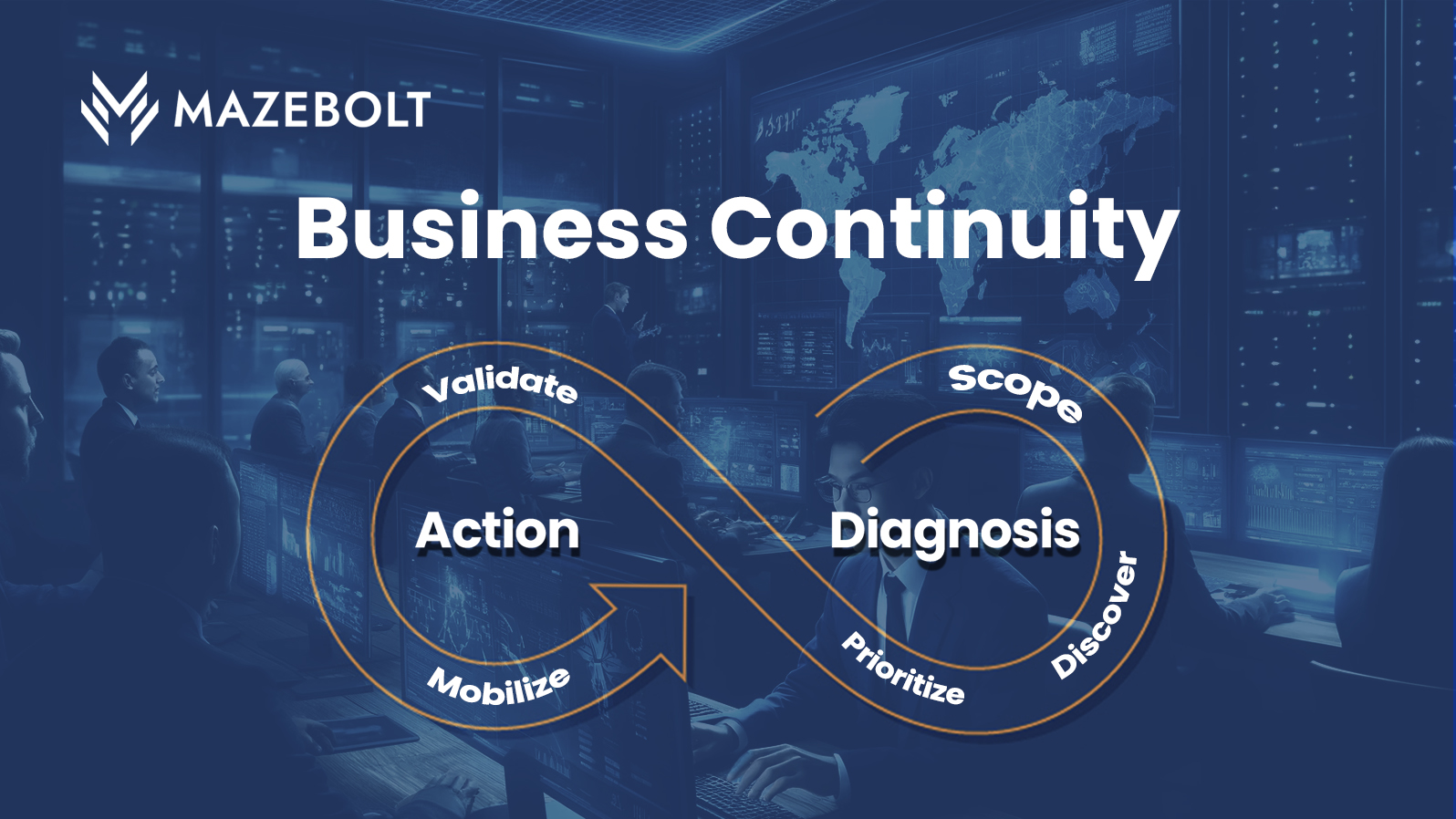
Put Business Continuity First with Continuous Threat Exposure Management (CTEM)

Strengthening Cyber-resilience in the Age of DORA
A Recap of 2023’s Most Formidable DDoS Attacks: A Year in Review
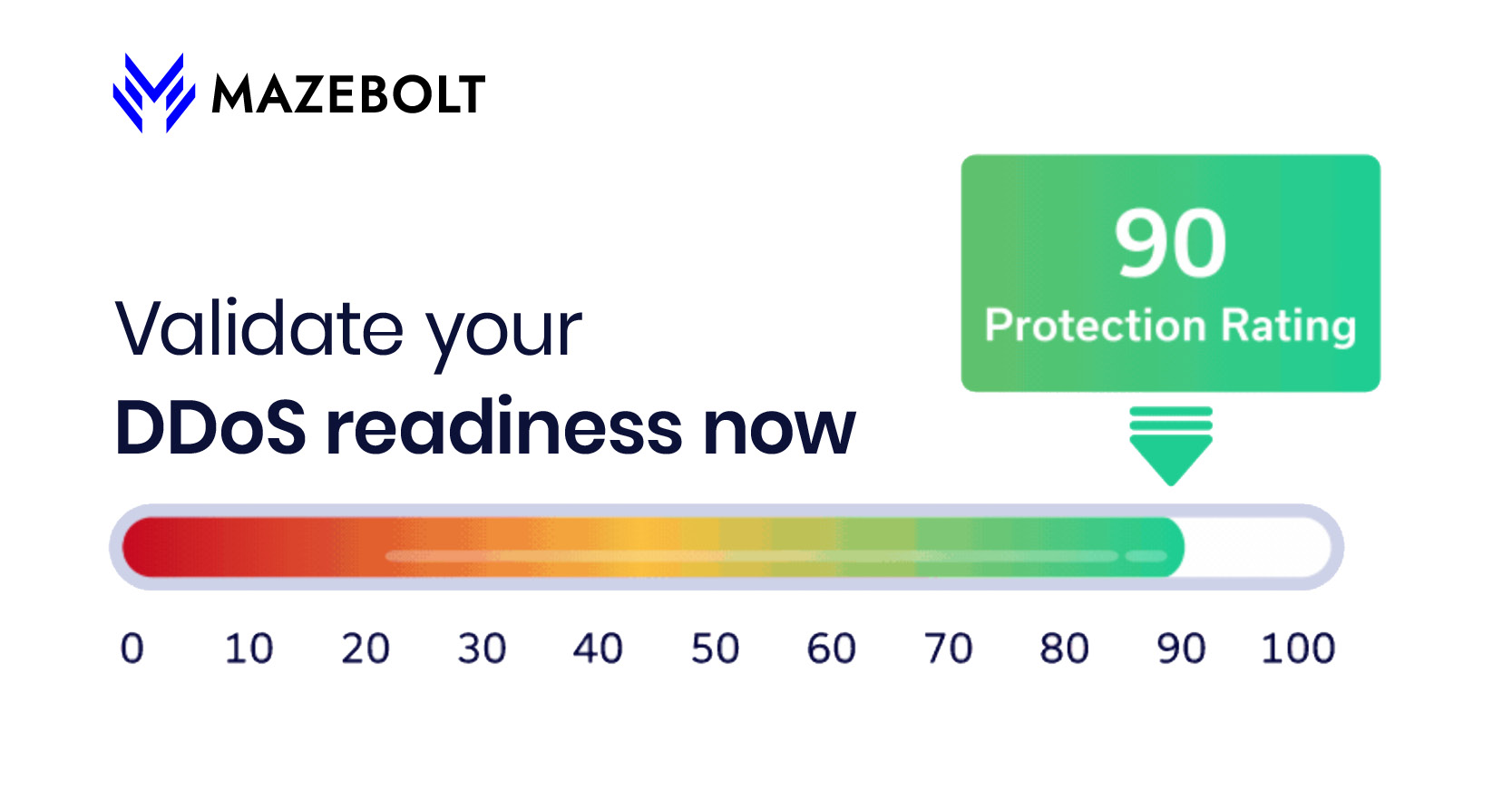
Unveiling DDoS Threat Rating (DTR)

Why do Fintech and DDoS Security Go Hand in Hand?

When DDoS is Just a Smoke Screen