Blog

F5 & MazeBolt: Proactively Eliminating DDoS Risk at Record Speed
F5 and MazeBolt eliminate DDoS risk with continuous testing and automated remediation across Layers 3, 4, and 7—at record speed.

Gamers vs. DDoS: Who Wins?
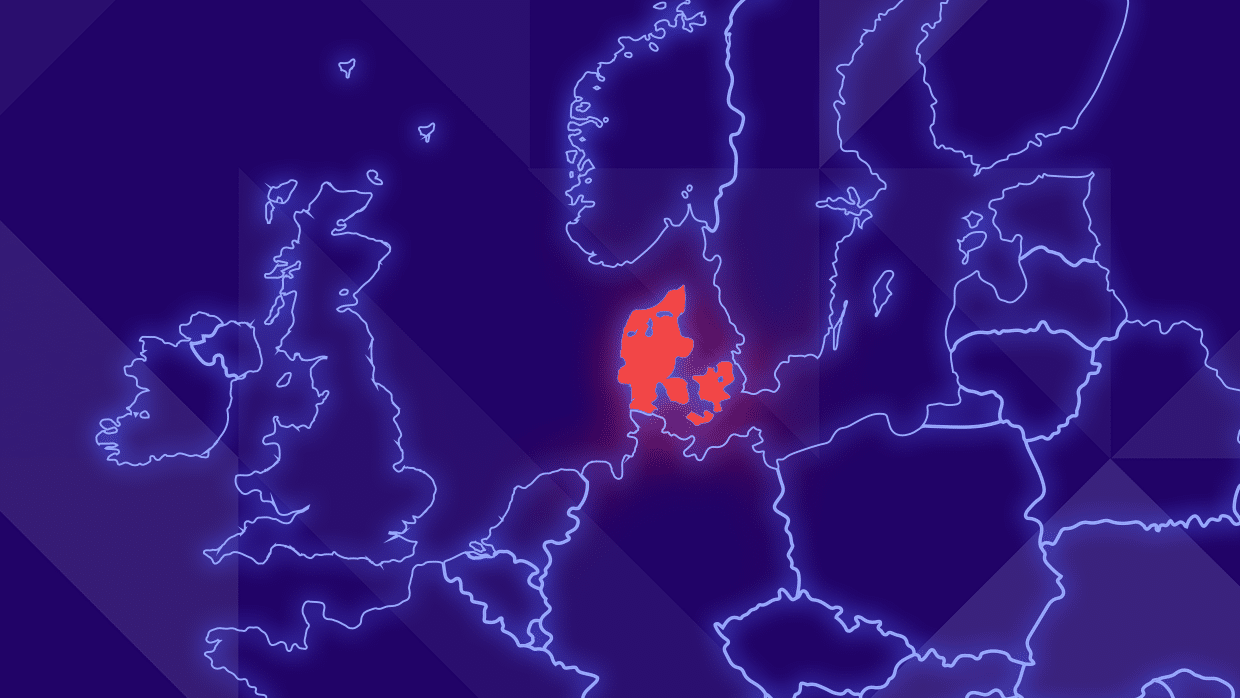
Denmark Suffers Coordinated DDoS Attacks on Government and Infrastructure

Polish Mobile Payment System BLIK Suffers Damaging DDoS Downtime

From Misconfiguration to Mitigation: A Step-By-Step Guide to Continuous DDoS Validation

Business Continuity at Risk: The True Cost of Skipping DDoS Vulnerability Testing

Black Friday DDoS Preparedness for Always-On Businesses

The Case for Automated, Continuous DDoS Testing: From Reactive Defense to Proactive Resilience

Quantifying Cyber Risk: Operational ROI for Continuous DDoS Testing

DDoS Resilience Survey – Insights from 300 Security Leaders

Defending Your DDoS Defenses

Red Team vs RADAR™: Closing the DDoS Protection Gap With 24/7 DDoS Validation