Blog

Advancing Enterprise DDoS Defense: MazeBolt RADAR’s 2024 Feature Review
2024 Year in Review: MazeBolt RADAR enhanced DDoS simulations, expanded attack coverage, improved performance, and added intuitive features for better security.

MazeBolt’s Security Blog is Now Among Top 100 Cyber Security Blogs
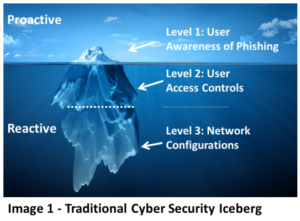
Importance of Proactive Feedback for DDoS Mitigation

DDoS Defenses – Newsletter February 2020

7 Reasons to Understand Your DDoS Kill Chain

Under DDoS Attack? Initiate these 5 Steps Immediately

Five reasons why your DDoS Mitigation might fail

Understanding Volumetric, Protocol, and Application Layer DDoS Attacks